Как заказать на кракене
Всё, что надо знать новичку. Onion - Fresh Onions, робот-проверяльщик и собиратель.onion-сайтов. "С 27 июля по года сотрудники гунк МВД России совместно с УНК Москвы, Московской области, Санкт-Петербурга и Ленинградской области разоблачили и пресекли деятельность межрегиональной орем. Годнотаба - список ссылок с onion зоны. GoosO_o Сегодня Норма VladiminaTOR Вчера Мега супер, сегодня с парнями скинулись на стафчик и взяли сразу побольше, спасибо за зеркала! Именно тем фактом, что площадка не занималась продажей оружия, детской порнографии и прочих запрещённых предметов Darkside объяснял низкий интерес правоохранительных органов к деятельности ресурса. Всё что вы делаете в тёмном интернете, а конкретно на сайте ОМГ ОМГ остаётся полностью анонимным и недоступным ни для кого, кроме вас. Является зеркалом сайта fo в скрытой сети, проверен временем и bitcoin-сообществом. Onion - The Majestic Garden зарубежная торговая площадка в виде форума, открытая регистрация, много всяких плюшек в виде multisig, 2FA, существует уже пару лет. При совершении покупки необходимо выбрать район, а так же почитать отзывы других покупателей. Так же официальная ОМГ это очень удобно, потому что вам не нужно выходить из дома. Что можно купить на Гидре Если кратко всевозможные запрещенные товары. Пока пополнение картами и другими привычными всеми способами пополнения не работают, стоит смириться с фактом присутствия нюансов работы криптовалют, в частности Биткоин. Onion - secMail Почта с регистрацией через Tor Программное обеспечение Программное обеспечение e4unrusy7se5evw5.onion - eXeLaB, портал по исследованию программ. Тогда как через qiwi все абсолютно анонимно. Форумы. В противном случае работа будет осуществляться очень медленно. Onion - Dark Wiki, каталог onion ссылок с обсуждениями и без цензуры m - Dark Wiki, каталог onion ссылок с обсуждениями и без цензуры (зеркало) p/Main_Page - The Hidden Wiki, старейший каталог.onion-ресурсов, рассадник мошеннических ссылок. Действует на основании федерального закона от года 187-ФЗ «О внесении изменений в отдельные законодательные акты Российской Федерации по вопросам защиты интеллектуальных прав в информационно-телекоммуникационных сетях». Требует включенный JavaScript. Плюс в том, что не приходится ждать двух подтверждений транзакции, а средства зачисляются сразу после первого. p/tor/192-sajty-seti-tor-poisk-v-darknet-sajty-tor2 *источники ссылок http doe6ypf2fcyznaq5.onion, / *просим сообщать о нерабочих ссылках внизу в комментариях! Не работает без JavaScript. ( зеркала и аналоги The Hidden Wiki) Сайты со списками ссылок Tor ( зеркала и аналоги The Hidden Wiki) torlinkbgs6aabns. Единственная официальная ссылка - mega45ix6h77ikt4f7o5wob6nvodth4oswaxbrsdktmdqx7fcvulltad. Иногда отключается на несколько часов. Этот сайт упоминается в деловой социальной сети LinkedIn 0 раз. Веб-сайты в Dark Web переходят с v2 на v3 Onion. . Onion - 24xbtc обменка, большое количество направлений обмена электронных валют Jabber / xmpp Jabber / xmpp torxmppu5u7amsed. Клёво12 Плохо Рейтинг.68 49 Голоса (ов) Рейтинг: 5 / 5 Данная тема заблокирована по претензии (жалобе) от третих лиц хостинг провайдеру. Внутри kragl ничего нет. Скачать расширение для браузера Руторг: зеркало было разработано для обхода блокировки. "Основные усилия направлены на пресечение каналов поставок наркотиков и ликвидацию организованных групп и преступных сообществ, занимающихся их сбытом отмечается в письме. Видно число проведенных сделок в профиле. Onion - Autistici древний и надежный комплекс всяких штук для анона: VPN, email, jabber и даже блоги. Как мы знаем "рынок не терпит пустоты" и в теневом интернет пространстве стали набирать популярность два других аналогичных сайта, которые уже существовали до закрытия Hydra. Onion - Ящик, сервис обмена сообщениями. Уважаемые дамы и господа! Форум Меге это же отличное место находить общие знакомства в совместных интересах, заводить, может быть, какие-то деловые связи. Что-то про аниме-картинки пок-пок-пок. Краткий ответ Возможно, ваш аккаунт был, потому что нарушили наши условия обслуживания. Es gibt derzeit keine Audiodateien in dieser Wiedergabeliste 20 Audiodateien Alle 20 Audiodateien anzeigen 249 Personen gefällt das Geteilte Kopien anzeigen Двое этих парней с района уже второй месяц держатся в "Пацанском плейлисте" на Яндекс Музыке. Просто покидали народ в очередной раз, кстати такая тенденция длилась больше 3 лет. Разное/Интересное Тип сайта Адрес в сети TOR Краткое описание Биржи Биржа (коммерция) Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылзии. Onion - крупнейшая на сегодня торговая площадка в русскоязычном сегменте сети Tor. Как зайти 2021. Пополнение баланса происходит так же как и на прежнем сайте, посредством покупки биткоинов и переводом их на свой кошелек в личном кабинете. Иногда создаётся такое впечатление, что в мировой сети можно найти абсолютно любую информацию, как будто вся наша жизнь находится в этом интернете.
Как заказать на кракене - Кракен сайт официальный ссылка kraken clear com
�и это магазин закладок. Вход Для входа на Мега нужно правильно ввести пару логин-пароль, а затем разгадать капчу. Отключив серверы маркета, немецкие силовики также изъяли и крупную сумму в криптовалюте. Например, легендарный браузер Tor, не так давно появившийся в сериале «Карточный домик» в качестве средства для контакта с «тёмным интернетом без проблем преодолевает любые блокировки. Пожелаем им удачи, а сами займёмся более благодарным делом. Onion - Neboard имиджборд без капчи, вместо которой используется PoW. Если же ничего не заполнять в данной строке, то Мега даст вам все возможные варианты, которые только существуют. У каждого сайта всегда есть круг конкурентов, и чтобы расти над ними, исследуйте их и будьте на шаг впереди. Клёво12 Плохо Рейтинг.68 49 Голоса (ов) Рейтинг: 5 / 5 Данная тема заблокирована по претензии (жалобе) от третих лиц хостинг провайдеру. Что можно купить на Гидре Если кратко всевозможные запрещенные товары. Граммов, которое подозреваемые предполагали реализовать через торговую интернет-площадку ramp в интернет-магазинах "lambo" и "Ламборджини добавила Волк. Например, такая интересная уловка, как замена ссылки. Ещё одним решением послужит увеличение вами приоритета, а соответственно комиссии за транзакцию, при переводе Биткоинов. Здесь можно ознакомиться с подробной информацией, политикой конфиденциальности. Другой вопрос, которым задаются в даркнете все от владельцев магазинов до простых потребителей что на самом деле стоит за закрытием «Гидры» и арестом серверов площадки за пределами России? В октябре 2021. Всегда смотрите на адресную строку браузера, так вы сделаете все правильно! 2qrdpvonwwqnic7j.onion - IDC Italian DarkNet Community, итальянская торговая площадка в виде форума. Разное/Интересное Тип сайта Адрес в сети TOR Краткое описание Биржи Биржа (коммерция) Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылзии. Kp6yw42wb5wpsd6n.onion - Minerva зарубежная торговая площадка, обещают некое двойное шифрование ваших данных, присутствует multisig wallets, саппорт для разрешения ситуаций. В некоторых случаях поисковые системы считают дублированное содержание, как обман и манипуляцию и могут принимать санкции. Хорошая новость, для любых транзакций имеется встроенное 7dxhash шифрование, его нельзя перехватить по воздуху, поймать через wifi или Ethernet. Он несколько замедляет работу браузера, обещая при этом «бесплатное полное шифрование трафика а для его активации требуется ввести адрес электронной почты. Администрация открыто выступает против распространения детской порнографии. Onion - Acropolis некая зарубежная торговая площадочка, описания собственно и нет, пробуйте, отписывайтесь. Onion - Схоронил! . Вместо курьера вы получите адрес и описание места где забрать заказ. Напоминает slack 7qzmtqy2itl7dwuu. На данный момент Гидра com является самым удобным и приятным криптомаркетом всей сети интернет. Книжная купить по выгодной цене на АлиЭкпресс. Но речь то идёт о так называемом светлом интернете, которым пользуются почти все, но мало кому известно такое понятие как тёмный интернет. Является зеркалом сайта fo в скрытой сети, проверен временем и bitcoin-сообществом. Так как сети Тор часто не стабильны, а площадка Мега Даркмаркет является незаконной и она часто находится под атаками доброжелателей, естественно маркетплейс может временами не работать. Для этого достаточно воспользоваться специальным сервисом. Видно число проведенных сделок в профиле. А если вы не хотите переживать, а хотите быть максимально уверенным в своей покупке, то выбирайте предварительный заказ! Залетайте пацаны, проверено! Zerobinqmdqd236y.onion - ZeroBin безопасный pastebin с шифрованием, требует javascript, к сожалению pastagdsp33j7aoq. Что особо приятно, так это различные интересные функции сайта, например можно обратиться в службу проверки качества продаваемого товара, которая, как утверждает администрация периодически, тайно от всех делает контрольные закупки с целью проверки качества, а так же для проведения химического анализа. Onion - PekarMarket Сервис работает как биржа для покупки и продажи доступов к сайтам (webshells) с возможностью выбора по большому числу параметров.
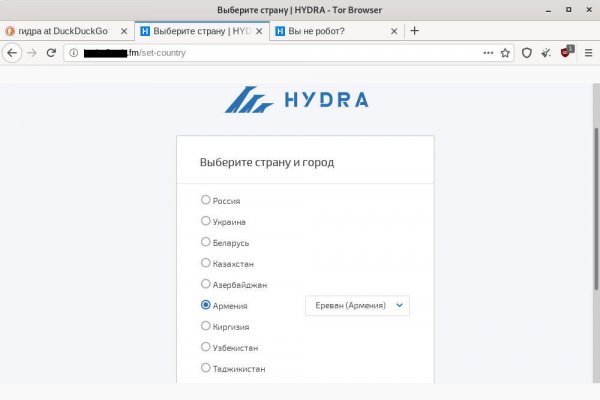
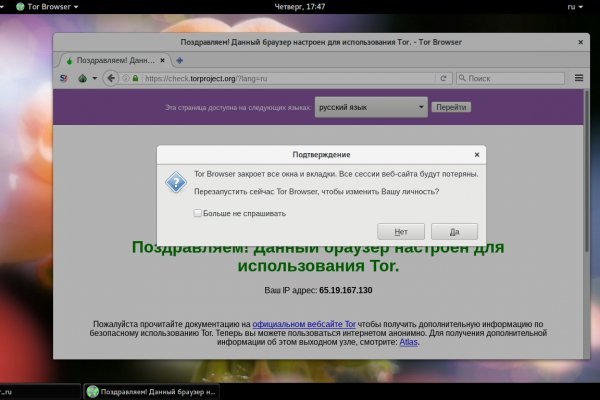
Располагается в темной части интернета, в сети Tor. Онлайн системы платежей: Не работают! Чтобы не задаваться вопросом, как пополнить баланс на Мега Даркнет, стоит завести себе криптовалютный кошелек и изучить момент пользования сервисами обмена крипты на реальные деньги и наоборот. Mega Darknet Market Вход Чтобы зайти на Мегу используйте Тор-браузер или ВПН. Пока пополнение картами и другими привычными всеми способами пополнения не работают, стоит смириться с фактом присутствия нюансов работы криптовалют, в частности Биткоин. Тогда как через qiwi все абсолютно анонимно. Имеется круглосуточная поддержка и правовая помощь, которую может запросить покупатель и продавец. Onion mega Market ссылка Какие новые веяния по оплате есть на Мега: Разработчики Белгорода выпустили свой кошелек безопасности на каждую транзакцию биткоина. Но обещают добавить Visa, Master Card, Maestro. Ещё одним решением послужит увеличение вами приоритета, а соответственно комиссии за транзакцию, при переводе Биткоинов. Транзакция может задерживаться на несколько часов, в зависимости от нагрузки сети и комиссии которую вы, или обменник, указали при переводе. Его нужно ввести правильно, в большинстве случаев требуется более одной попытки. Но сходство элементов дизайна присутствует всегда. Также многие используют XMR, считая ее самой безопасной и анонимной. Ссылка на мегу. Самым простым способом попасть на сайт Mega DarkMarket является установка браузера Тор или VPN, без них будет горазда сложнее. Важно понимать, на экранах мобильной версии и ПК версии, сайт магазина выглядит по-разному. Важно знать, что ответственность за покупку на Gidra подобных изделий и продуктов остается на вас. Заходите через анонимный браузер TOR с включенным VPN. Подробнее: Криптовалютные кошельки: Биткоин, Ефириум, и другие малоизвестные кошельки Банковские карты: Отсутствуют! Заполните соответствующую форму и разгадайте хитрую капчу для входа в личный аккаунт: Чтобы проверочный код входа приобрёл более человеческий вид, потяните за голубой ползунок до тех пор пока не увидите знакомые символы.